Remaining anonymous is often an important concern for OSINT practitioners. There are many types of OSINT, and many different reasons why we do not necessarily want our subjects to know we are trying to find out about them. A recruiter may not want a company to know that they are trying to lure away one of their staff members, or a penetration tester might want to research a spearphishing target without being noticed. There are many other cases where it is better to be anonymous when conducting OSINT investigations although to be clear it is never possible to be truly anonymous. Instead it is better to think about being pseudonymous when conducting OSINT enquiries. The purpose of this article is to look at some of the ways OSINT practitioners can still be uniquely identifiable despite the use of sock puppets, and why a digital fingerprint should be part of any pseudonym.

The issue of online pseudonyms for OSINT also intersects with the wider issue of online privacy. Amazon, Google, Facebook – and countless others – track and analyse most of our web movements for marketing purposes. Unless you are very proactive about privacy, most of your online activity is available to be collected, analysed, sold, and then re-sold. If you are an EU citizen then even GDPR offers very little real protection from this kind of intrusive data-gathering.
So what has this got to do with OSINT? Quite a lot in fact. The ability of web companies to gather data about you and your device means that any efforts to remain pseudonymous can easily be undone. If you log in to your Facebook sock puppet account, and then logout and switch to your personal account (or another sock puppet), the entire process is completely transparent to Facebook, who are then able to make associations between your real and false personas.
The purpose of the rest of this blog post is to look at how we leak information during OSINT investigations and how this can be mitigated. (Jake Creps and Matthias Wilson have already written some really good how-to articles on sock puppets).
IP Address
When you connect to the internet, your computer has a unique public IP address that is disclosed to the websites that you visit. This is fairly well known and a common Opsec practice is either to use Tor or a VPN to disguise your true IP address. This can be effective but it has many limitations: using the Tor Browser limits the functionality of many websites, and everyone can see that you’re using Tor, even they do not know who you are. The result is that you”ll spend a lot of time doing these instead of researching:
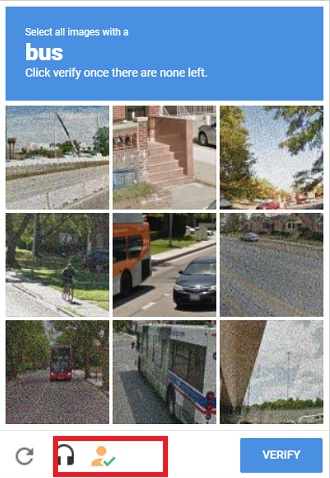
VPNs are another alternative, although again they have some limitations. Some VPN providers are not necessarily transparent about who owns them or what they do with your data, and as with TOR, many VPN IP addresses are well-known and are often blacklisted so that you’ll either have to fill in endless captchas before accessing the content you need. A good VPN service is an important tool for good Opsec, but neither Tor or VPNs are magic tools that mean you don’t have to pay attention to other areas.
I’d also argue that an IP address is not necessarily that important to a data surveillance company like Google or Amazon. Depending on how and where you access the web your IP address may regularly change or may be shared with many other people, so it is of limited value to an organisation that wants to know exactly who you are and what you like to do on the internet. This doesn’t mean that you shouldn’t consider what your IP address might reveal about you, but it’s important to be aware that it is not the complete picture.
Cookies & Cookie Auto-Delete
Cookies are also a well-known tracking method. There are different types of cookie, but the main threat to your sock puppet activities is that cookies can track you across the web long after you visited the website that they came from. Apart from the privacy aspect, the threat to your opsec is quite obvious. Cookies do not care that you’ve finished your enquiries and now you’re just going to do some personal browsing; they will still continue to track you across the web to build up a profile of your habits. The threat your OSINT work is quite obvious.
Here’s an example with LinkedIn, which is one of the most aggressive sites on the web for tracking. Before visiting the site, I cleared out my cookies and then tried to visit again. LinkedIn doesn’t like this because it no longer recognises who I am (even though my IP address remained the same):
After logging in, my browser plugins light up like a Christmas Tree:

Without even clicking on anything on the webpage, LinkedIn tries to load a large number of scripts and cookies, mostly with the intention of tracking my behaviour and trying to learn as much as possible about my online activities. If I switched from my real LinkedIn account to a sock puppet account, it would be quite obvious to LinkedIn what I was doing, and by extension to anyone else who runs a website with similar tracking capabilities. This is how the marketing company that know what groceries you buy also know what kind of porn websites you visit.
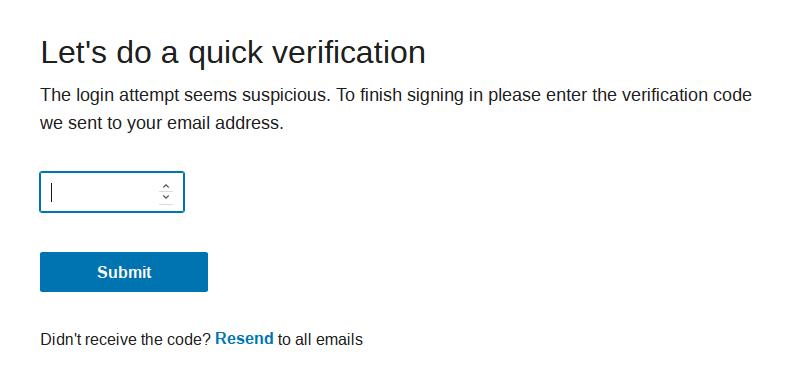
There are several ways to mitigate this by using the three tools pictured above. UBlock Origin (available for Firefox and Chrome) filters requests to display adverts and prevents your browser from retrieving and displaying marketing content. Privacy Badger (Firefox and Chrome) works to identify and block trackers. In this case it detected and blocked no fewer than 10 different tracking scripts on my LinkedIn homepage:
My preferred tool for dealing with intrusive tracking by cookies is to use Cookie Auto-Delete. It does not prevent cookies from being downloaded by the browser, but it ensures that when a browser tab is closed, any cookies associated with that tab are deleted. This prevents cookies from being able to track you across your browsing session and so disguises your web activity from sites that wish to track you. Cookie Auto-Delete is available for Firefox and Chrome.
Browser Fingerprinting
Browser Fingerprinting is a much newer tracking concept than either IP addresses or cookies. It is not as well-known but it is far more intrusive and thus presents a much bigger challenge to OSINT practitioners who wish to remain discreet. There’s a great academic paper that outlines some research in this area, but the basic premise of browser fingerprinting is that it is possible to combine the unique features of your browser and computer and combine them into a value that is unique and which can then be used to track you across the web. By looking at information like your browser software version, operating system, system fonts, graphics card, screen resolution, and many other variables, it is possible to build a unique browser “fingerprint” that can then be used to track you across the web. It is much more effective and persistent than either an IP address or cookies when it comes to tracking.
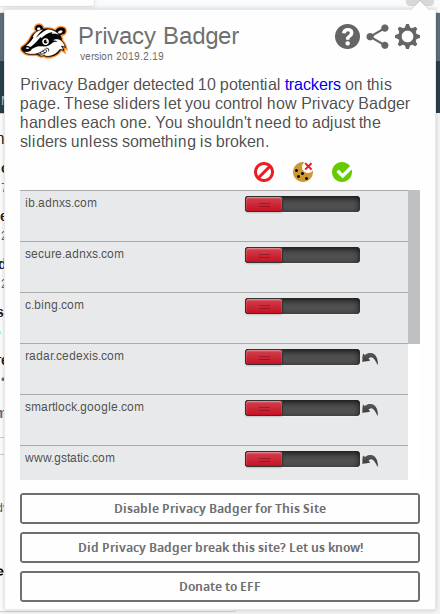
There are several good tools for analysing your own browser fingerprint. My two favourites are the EFF’s Panopticlick Tool, and the BrowserLeaks website. To demonstrate how the process works, I’m going to look at my own browser fingerprint “as is” without any addons, and then it is possible to see how to successfully obscure one’s online fingerprint for the purposes of pseudonymity.
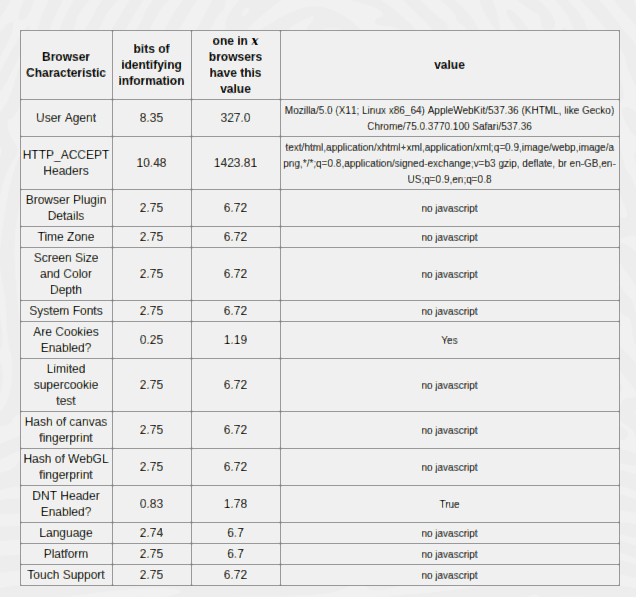
This is the first result from Panopticlick when scanning a fresh install of Chrome on Linux Mint 18.3:
With a clean Chrome installation with default settings, this was the result:
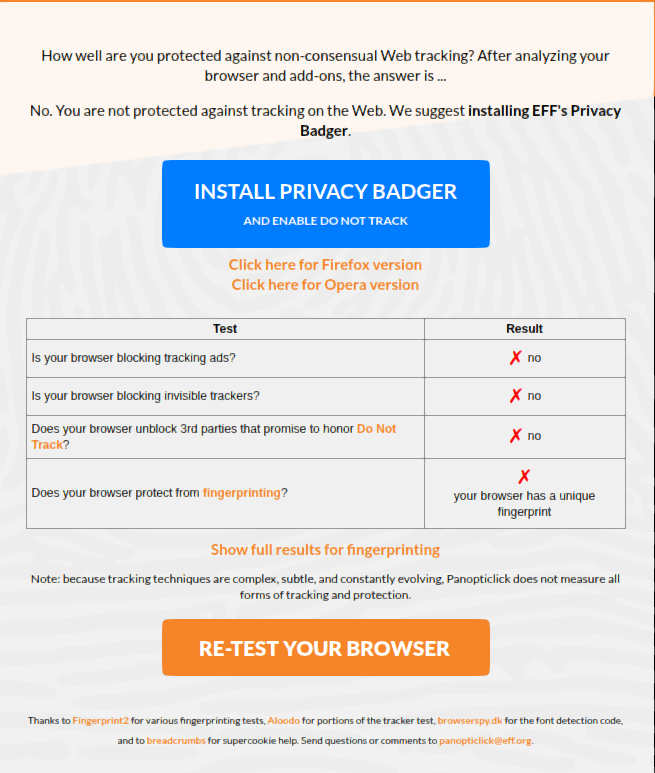
Not only am I not protected from tracking at all, but my browser has a unique fingerprint that will make me easily identifiable. There’s more detail about what this mean below:
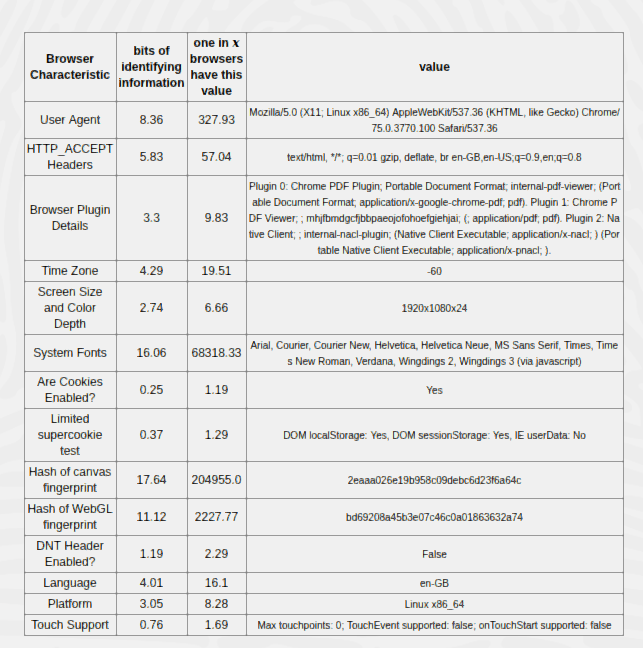
Panopticlick looks at how my browser settings appear to a website and then calculates how probable it is that anyone else has the exact same settings. The bits of identifying information is based on some fairly complicated mathematics that assesses how likely it is that any given fact is true of any one person. You can read more about that here, but in simple terms this is a score on a scale of 1 to 33, with 33 being completely unique. The Chrome default browser plugins I have are very common (3.3) but the hash of my canvas fingerprint (17.64) is not.
The third column expresses the same information in a different way by looking at how many browsers would typically share the same information. In this case it shows that 1 in 19.51 browsers are in the same timezone as me, 1 in 1.19 have cookies enabled, but only 1 in 204,955 browsers have the same canvas fingerprint as me. This means that my canvas fingerprint makes me extremely distinctive to anyone who wishes to identify me when I visit their website, regardless of which account I use to log in.
From an OSINT perspective this means that it doesn’t matter what my IP address is or even whether I clear out my cookies, as long as my hardware and browser setup remains the same, it is always obvious to a website who I am, regardless of how many sock puppet accounts I create. This is one of the ways in which Facebook and other sites are able to quickly identify multiple accounts that are run from the same machine, and therefore more likely to be bots or sock puppets.
Fortunately with a few tools and a bit of tweaking it is possible to change the way a browser appears to the internet. I installed and enabled UBlock Origin to block ads/trackers, Privacy Badger to block tracking scripts, and NoScript to disable any unwanted JavaScript from running. Here are the new results:
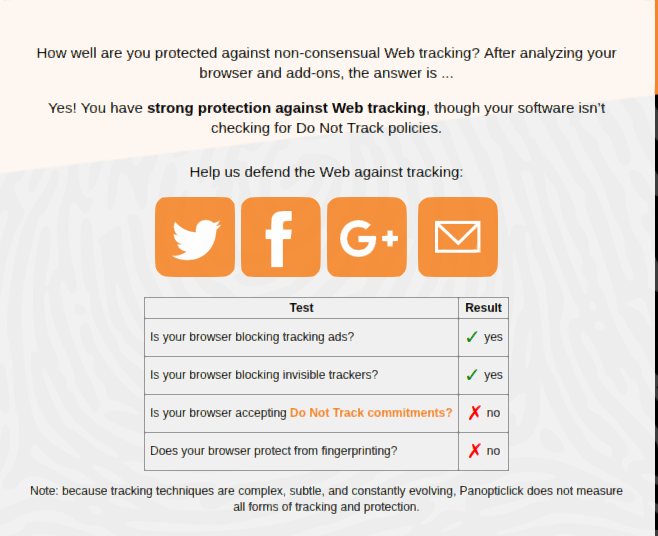
So already there is a little bit of progress – my browser now blocks tracking ads and trackers. An important point to note is that even though I told Chrome to send a Do Not Track request in the settings, it made no difference.
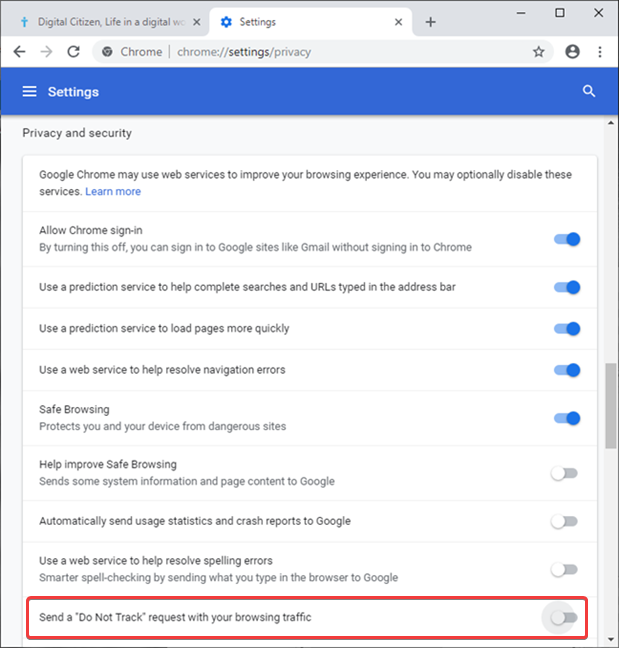
This reflects the reality that a request is just that – a request. The evidence suggests that most companies completely ignore them anyway, so they cannot be relied upon as a privacy setting. But what about the other fingerprint results?
I’m no longer a unique and special snowflake. By installing NoScript almost none of the browser-fingerprinting data points can be read by the website. NoScript prevents JavaScript from running, and since most of the fingerprinting tools rely on JavaScript, they stop working and can’t report back on who I am.

There is a downside to this though: NoScript is sometimes too powerful and it requires a lot of tweaking to get right. JavaScript is still needed for most modern websites to function correctly so using NoScript can cause a lot of pages to break. It’s possible to disable/enable individual scripts as needed so you’ll need to be patient to get everything running smoothly, but it’s very effective as an anti-fingerprinting tool.
User Agent
Your browser also sends information about itself to websites that it connects to. One of the pieces of information it supplies is the User Agent String which contains information about your browser and operating system. If I point my Chrome installation at What Is My User Agent? I get this result:
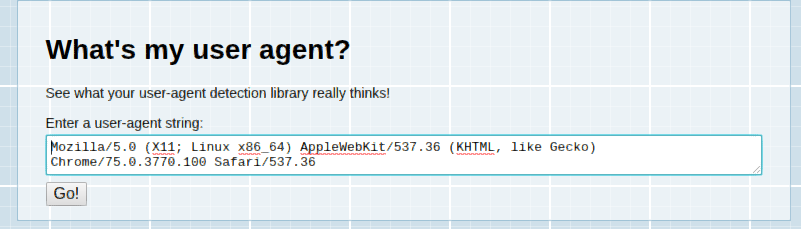
It correctly says that I’m running Chrome 75.0.3770.100 on a Linuz x86_64 system. The other browser technology mentioned in the UA string is about compatibility rather than the actual browser I’m using – the references to AppleWebKit and Gecko are supplying information about what kind of software my browser is compatible with, so that the website knows how to display content correctly. This is the main legitimate reason that User Agent Strings exist, but the downside from a privacy point of view is that they are also another data point that can be used to identify you.
To counter this it is possible to use a simple User Agent Switcher addon. This tells a website that you’re using a different kind of browser to the one that you really are using, and so your real browser details are obfuscated. Once installed in Firefox or Chrome a User Agent Switcher allows your browser to effectively impersonate another browser or operating system. After installing it in Chrome, I selected the Android User Agent string and checked it on whatismybrowser.com:
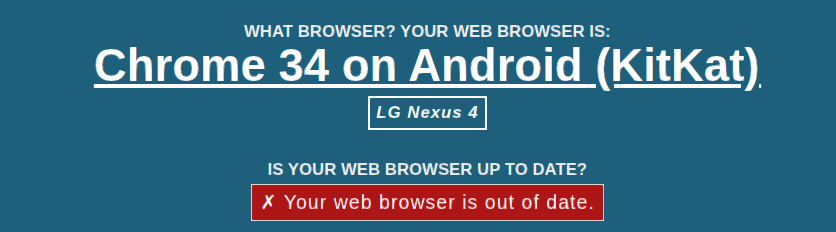
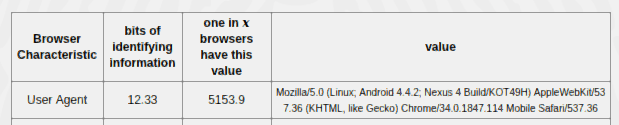
To a website I now appear to be running on a completely different device and operating system. My Panopticlick footprint now shows the same change:
This emphasises an important point about anonymity and pseudonymity online. You can never by truly anonymous when conducting OSINT. You have to present some kind of User Agent String to a website, so better to present a false one rather than aim for none at all.
Canvas Fingerprint

The most potent aspect of browser fingerprinting is the canvas fingerprint. This list of sites that are known to use canvas fingerprinting is long and is very out of date, so the real number of sites using canvas fingerprinting is probably much larger. Canvas fingerprinting works by taking information about the way your browser displays fonts and graphics and then combines them into a unique hash that can be used to identify you. The combination of your operating system, graphics card and drivers, system fonts, screen resolution and other variables are unique enough for them to be combined into a single hash. This hash is your computer’s unique digital fingerprint and websites use to recognise you. Even if you’ve made really good sock puppets, if you run all the accounts from the same machine then they all look identical to a company that uses canvas fingerprinting to monitor user activity.
Panopticlick can show what a canvas fingerprint hash looks like. I’ve run the test again (with NoScript disabled):
![]()
When I load the page, Panopticlick serves a tiny image to my browser and then watches what happens when my browser tries to render it. The value of this calculation is presented as a hash: 2eaaa026e19b958c09debc6d23f6a64c.
This means nothing to a human but it makes me uniquely identifiable to anyone who runs a website with canvas fingerprinting enabled. Changing my IP address and clearing out my cookies will make no difference whatsoever to how I appear to the website that I’m trying to conduct OSINT research on. Switching from a real account to a sock puppet makes no difference either because the underlying hardware-software combination is the same. Facebook do not publicly explain how they detect suspected false accounts, but they definitely use canvas fingerprinting among many other techniques. I suspect this is partly why so many people having trouble creating long-lasting Facebook accounts for OSINT purposes.
So how could we counter this problem? As I’ve said already in this post, it is important to think about being pseudonymous and not anonymous. Instead of simply wishing we didn’t have a fingerprint and trying to hide it, it’s much easier just to report a false value. For this article I tested two Canvas Fingerprinting addons for Chrome: Canvas Fingerprint Defender and Canvas Blocker. When I re-run the Panopticlick test I get a new result:
![]()
Quite a difference! The anti-fingerprinting extensions mean that my browser looks very common and does not stand out as much. It now shares characteristics with 1 in 41.99 browsers, not 1 in 103,142 like before. Instead of presenting a unique hash back to the website, my browser presents a random value instead so it is not possible to trace me around the web as easily.
I should point out that I also tried Canvas Defender, but it made no difference in either Panopticlick or BrowserLeaks. For Firefox I recommend CanvasBlocker, Canvas Fingerprint Defender, or Canvas Blocker.
Conclusion
I hope that it’s clear from this article that to effectively create a truly effective OSINT sock puppet account requires more than just a VPN along with a false name and a random photo. How we appear to websites and the massive data companies behind them also has to be taken into consideration when carrying out OSINT tasks.
There’s a lot more to the subject of course but here are some additional resources that are useful:

Additional resource: https://www.deviceinfo.me
I’m a fan of using different browsers and learning to switch between them (plus of course tightening the privacy and security settings in the browsers). I’d typically use FF, Chromium, Brave, … Another good habit is using virtual machines, again with various browsers. Also, my FF is set up in a way that it deletes browsing data when closed. I do that every now and then. I find this better for me since I also like to keep as few add-ons as possible (they might slow the experience a bit).