Discovering email addresses or user names is an important part of OSINT work. In this short article I’ll look at three methods for gathering information about Gmail users.
How To Tell If An Organisation Uses Gmail
The growth of GSuite (now better known as Google Workspace) for cloud based productivity means that organisations can link their own domain to their business Gmail account. This means that email addreses don’t have to end in @gmail.com in order to be valid Gmail addresses. If ACME Business Solutions link their domain acmebusinesssolutions.com to GSuite, then [email protected] will also be a valid Gmail address too.
Checking the DNS MX and TXT records for an organisation’s domain will indicate whether or not the company uses Gmail. In this example I’ve used ViewDNS to look up the DNS records for The Daily Telegraph (telegraph.co.uk):
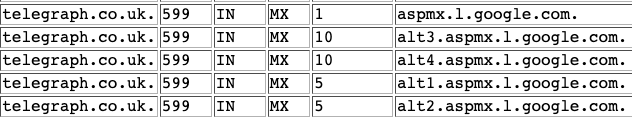
MX records describe how a domain handles email. For The Telegraph we can see that their MX records point to Google servers, so we know that any email that ends with @telegraph.co.uk will be using Gmail.
There’s a clue in the TXT records too. Domains protect themeselves being used for email spoofing by adding an SPF entry to their TXT records. An SPF record lists the IP address and other domains that are authorised to send email on behalf of the main domain, so it is helpful for revealing parts of a company’s services and infrastructure that may not always be apparent.
The Telegraph’s SPF record looks like this:
"v=spf1 a mx ip4:195.162.12.4 ip4:31.121.182.66 include:amazonses.com include:_spf.google.com ~all"The line include:_spf.google.com tells us that The Telegraph has authorised Google to send emails on its behalf – which means that it is using Gmail.
How To Tell If A User Has A Gmail Account
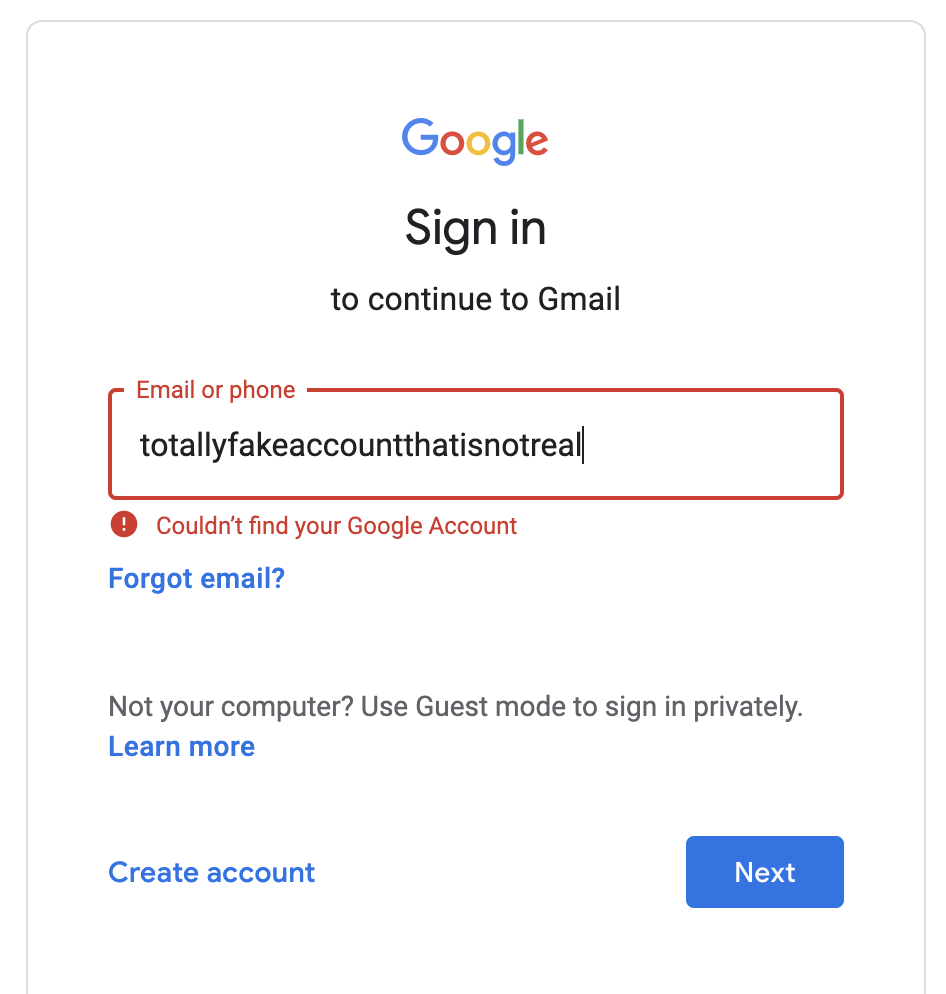
This technique is a little more direct and is definitely an active form of OSINT and caution needs to be exercised. Google’s security around identity and access is very good and if you spam this technique you will have to solve a lot of captchas. It’s simply a case of entering a username or email address at the Google login portal and see what results are returned.
Plain usernames can be used if you’re looking for a Gmail address. For a Gmail address that uses another domain (as in the Telegraph example above) you need to enter the full email address.
If the account does not exist, you’ll get a “Couldn’t find your Google Account” error. If the account does exist, you’ll be prompted for the password.
A word of warning though – anything further than this is likely to be a criminal offence in most countries. Unless you have permission to access the account (for example as part of a penetration test) then you should not do this.
Query A Google URL To Verify If A User Has A Gmail Account
This is much better and more reliable than messing around with login portals. We can use Curl to query a specific Google URL to see if a Gmail address exists or not. It’s also worth remembering that the first part of a Gmail address is the same as the username for other Google services like YouTube, so this can be helpful for user enumeration across other platforms.
All we need to do is pass an email address to this URL:
curl -v https://mail.google.com/mail/[email protected]
Curl returns a lot of data, but there’s an important difference between accounts that do and do not exist.
If a Gmail account exists, Curl will return a response with set-cookie in the results, like this:
*snip* < HTTP/2 204 < cache-control: no-cache, no-store, max-age=0, must-revalidate < pragma: no-cache < expires: Mon, 01 Jan 1990 00:00:00 GMT < date: <Today's date/time> < server: GSE < set-cookie: COMPASS=gmail=CrABAAlriVcIO1q9Mqjmg57v0Q2hgEtOI3grZtm4Dgly7w6s_0hENuYwNjFBUeFwX4HgPptDqPLpHB_kbitxtVwevcoYv7aFxxT3EEO_b8Vpuav3w-_cOiUHsVMvvy5SS6oIl etc...
If the account/user does not exist, there will be no set-cookie parameter in the results.
This feature was first reported to Google as a security bug in 2017 by the person who discovered it, but Google do not regard it as a security concern and the URL does not appear to be heavily rate-limited. This means that this technique is much easier to use for bulk user enumeration.